Due to the rapidly increasing threats to an IT operation, every company should survey and evaluate the relevant IT threats with regard to information security. However, the selection of threats for the primary InfoSec protection goals confidentiality, integrity and availability is very complex, because there are no simple threat lists, especially for small and medium-sized enterprises.
SEC4YOU has taken on this task and created the SEC4YOU Information Security Threat List 2022. In this article, the most important threats are presented and explained. Readers will get a sound overview of which threats you should have secured your company against, as these are now becoming a reality for companies on an almost daily basis.
What does an information security risk assessment accomplish?
In addition to the prevention of significant to existence-threatening economic and intangible damages, an information security risk assessment supports the selection of suitable InfoSec measures that are required to protect the company from the dangers. If you operate an ISMS according to ISO 27001 or TISAX®, the company must provide documented evidence of the complete risk assessment, including the risk method, the assessment criteria and the assessment.
Sources of information security threats
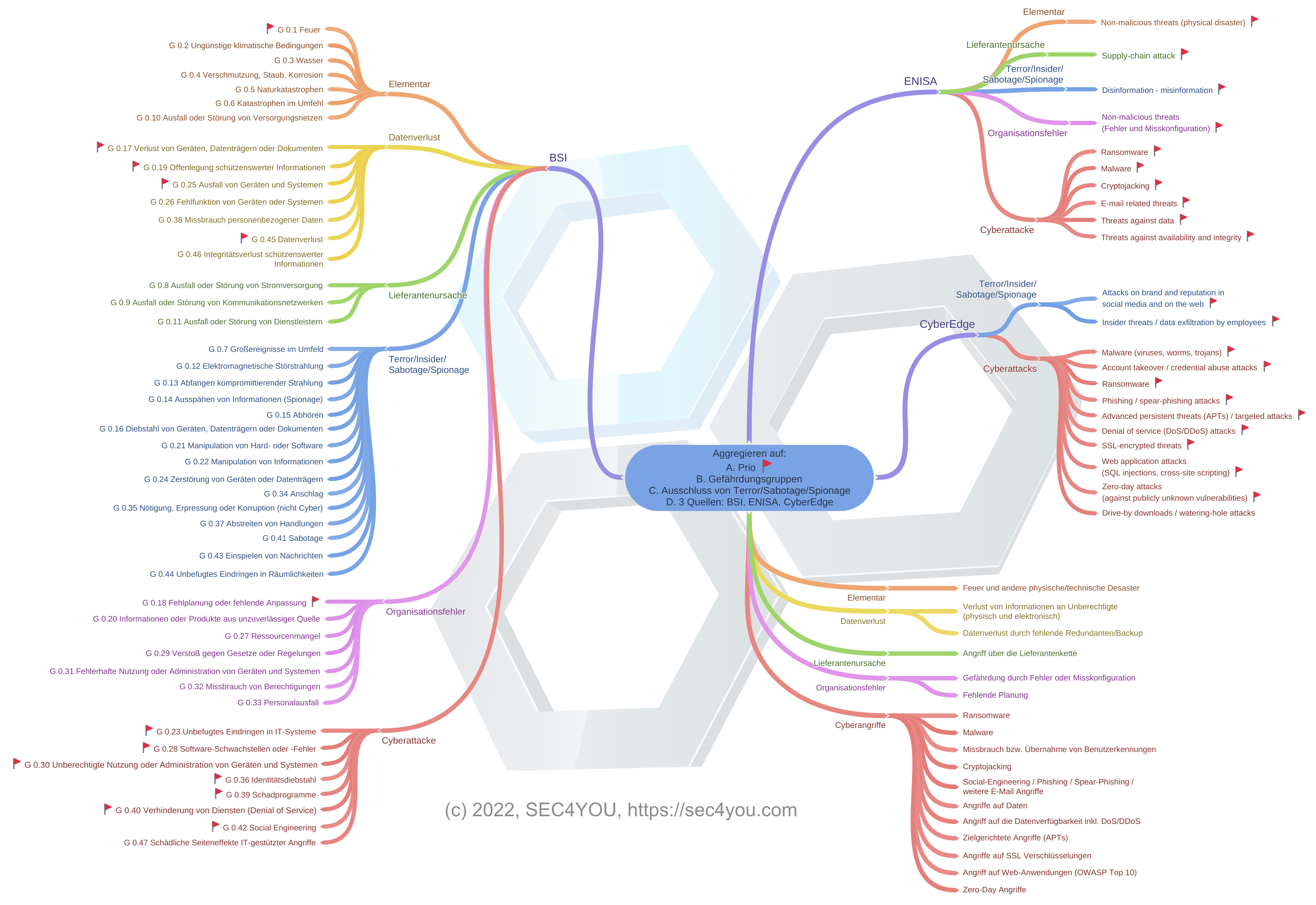
The following sources were used as the basis for the SEC4YOU Information Security Threat List 2022:

The 47 Elementary Threats of the German Federal Office for Information Security (BSI).
A very classic list that lists a variety of elementary threats and deals intensively with the aspects of sabotage/terror and espionage. Unfortunately, this publication does not adequately assess modern cyberattack vectors.
ENISA Threat Landscape 2021
A valuable information security assessment by the European Cybersecurity Agency that analyzes cybersecurity trends on 115 pages, describing the nine most significant threats and providing detailed recommendations on how to avoid them.

2022 Cyberthreat Defense Report by CyberEdge Group
This report highlights technologies and their resilience to cyberthreats, in addition the report provides an excellent assessment of 12 cyberthreats that no risk assessment should be without.
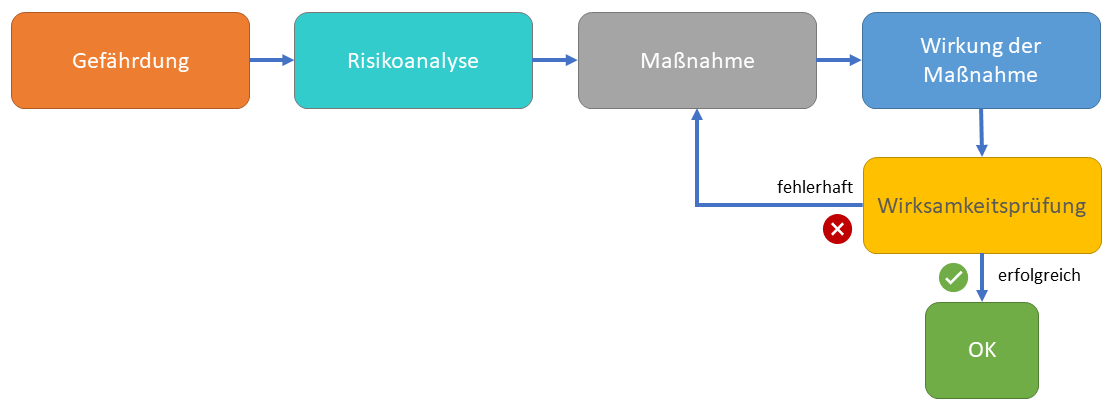
Clear distinction between hazard, measure, effect and effectiveness test
In an information security risk assessment, the CISO is required to actually assess the threats/hazards and only later determine the action and its potential impact, here using a simplified practical example of “malware” to delineate the terms:
- Threat: The risk that the company will be infected by malware.
- Measure:
- Full-coverage malware protection software on all endpoints with vendor A.
- Perimeter gateway protection and upload filters with manufacturer B
- Regular testing of internal and external services for weak points (vulnerabilities)
- Effect of the measure (the definition of effectiveness targets):
- Malware from the source Internet and e‑mail is reliably detected at the gateway.
- Malware from the source USB sticks and end-to-end encrypted emails is reliably detected at the end device.
- Effectiveness testing:
- Is there any indication that malware is not reliably detected at the gateway, upload filters or end devices?
- Is malware also detected in encrypted connections?
- If the effectiveness test shows that the measures are not effective, the measures must be optimized or expanded.
The SEC4YOU Methodology
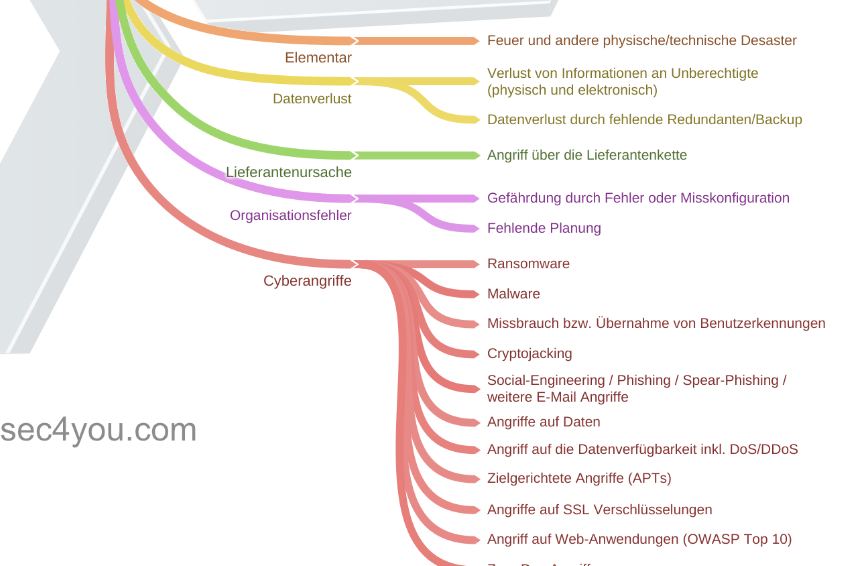
CyberEdge 2022 Cyberthreat Defense Report listed and prioritized. You can identify the priority of a threat by the red flag in the chart below.
We then classified the threats into the following categories: Elemental, Data Loss, Supplier Cause, Terror/Insider/Sabotage/Espionage, Organizational Error, Cyberattack.
We then filtered the prioritized threats from all 3 sources, but removed the terror/insider/sabotage/espionage category because it is not very relevant to a majority of companies.
The result: The SEC4YOU Information Security Threat List 2022
The following 17 threats were developed as the most significant threats to IT operations:
Elemental
1. Fire and other physical/technical disasters
Data loss
2. Loss of information to unauthorized parties (physical and electronic)
3. Loss of data due to lack of redundancy/backup
Supplier Cause
4. Attack through the supplier chain
Organizational error
5. Exposure due to errors or misconfiguration
6. Lack of planning
Cyber attacks
7. Ransomware
8. Malware
9. Misuse or hijacking of user IDs
10. Cryptojacking
11. Social engineering / phishing / spear phishing / other e‑mail attacks
12. Attacks on data
13. Attacks on data availability incl. DoS/DDoS
14. Targeted attacks (APTs)
15. Attacks on SSL encryption
16. Attacks on web applications (OWASP Top 10)
17. Zero-day attacks
Explanation of the threat list
As part of the information security risk assessment, evaluate the threat list with the asset groups and identify existing and additionally required technical and organizational measures. Use the explanations below to apply a risk assessment by impact and probability of occurrence.
1. Fire and other physical/technical disasters.
This is about natural disasters and local elemental hazards such as fire or water that can destroy IT infrastructures. However, technical defects in server rooms or in critical IT services that completely interrupt IT operations are also covered. Whether flood, fire or firefighting foam destroys the server rack, ensure redundancies and multiple data storage in time.
2. Loss of information to unauthorized persons (physical and electronic)
This threat is about the information itself. However, it does not matter whether an unauthorized person steals it as paper documents or it is copied electronically via remote access. The company-critical information in the hands of a competitor or the loss of reputation can cause lasting damage to the company.
3. Data loss due to lack of redundancy/backup
If critical IT services are not designed redundantly (including storage, virtualization platforms, domain controllers, directory services, DNS servers, web services), data loss can occur. Data loss can be caused by hardware defects, configuration errors or simply human error. In the end, a professionally planned and regularly tested backup solution helps prevent data loss.
4. Attack via the supply chain
In the “supply chain attack”, the trust between a (large) supplier and its customers is abused. Here, attackers can compromise the data and systems of one (or many) companies via remote access set up or credentials or keys stored with the supplier. In the past, however, a large proportion of attacks were carried out via compromised software from individual suppliers, where hackers were able to place targeted attack methods in supposedly trustworthy software updates.
5. Risk due to errors or misconfiguration
Servers and IT services are configured differently and sometimes insecurely, especially due to a lack of configuration specifications (hardening guidelines, configuration baselines) and a lack of automation. Also, subsequent security-relevant configuration adjustments are often not implemented by the IT teams of companies. Unfortunately, all too often software or services are put into operation with the default configurations and default access data, which can be easily exploited by attackers.
6. Lack of planning
Poorly planned IT infrastructures, improper maintenance and repair processes, underestimated IT migrations, procurement of IT systems with inadequate security features, poor resource planning, lack of spare parts, and even outdated transfer protocols can all be traced back to a lack of planning and poor project management. Only through early consideration of information security and stringent planning management are information security-relevant projects uncovered and can be planned and implemented according to criticality.
7. Ransomware
Is a special type of devious attack in which attackers encrypt corporate data and demand a ransom to make the data accessible again. Sometimes the attackers also steal the data and demand payments so that the data is not sent to authorities, competitors or the public. Phishing emails and remote desktop protocol (RDP) connections top the list of entry points for ransomware.
8. Malware
Malware is the umbrella term for software, firmware or code that maliciously affects the confidentiality, integrity or availability of systems. Subtypes include viruses, worms, Trojan horses, RATs (remote access tools), and code infections of systems. Some spyware and adware also count as malware. Good malware protection with runtime behavior analysis on all systems (clients, servers, gateways) helps to contain the infection and spread of malware. Installation of software and drivers by users on end devices should be massively restricted.
9. Misuse or takeover of user IDs
In the case of misuse of user IDs or identity theft, the attacker fakes the identity of a person in order to act on their behalf. This is particularly easy to do by hacking email accounts and then taking over other services via email-based password reset procedures. Strong passwords with additional two-factor authentication are the best protection against this threat. At the same time, companies need to educate users via security awareness campaigns about the use of unique passwords and the danger of phishing attacks.
10. Cryptojacking
The idea of crypto-mining on strong hardware is not new, but it becomes a crime to use the computing power and electricity of a victim. This equally affects end devices and also servers, which are infected and exploited by attackers. Occasionally, software manufacturers have also attempted to incorporate corresponding mining services into their software and plug-ins, arguing this with the free use of the software and disguising it in a long EULA.
11. Social engineering / phishing / spear phishing / other e‑mail attacks
The variance of threats through social engineering is large and includes pishing, spear phishing, whailing, smishing, vishing and in the future certainly also video phishing with deep fake technology. The infection medium e‑mail still plays the most important role. Companies are required to train all employees in the perfidious methods of social engineering attacks using current examples and their possible effects in regular security awareness campaigns and mandatory training courses.
12. Attacks on data
The dangers posed by attacks on data include unauthorized access, unwanted publication, false reporting / misinformation, disinformation (deliberately providing false information for the purpose of deception). Often referred to as a data breach / data leak, these incidents always refer to the publication of sensitive, confidential or proprietary data in an untrusted environment. Particular criticality arises when the data breach involves personal data as defined by the GDPR. Then the company must report this data breach to the authority.
13. Attack against data availability incl. DoS/DDoS.
Attacks against data availability focus on two attack methods: distributed denial of service (DDoS) and attacks on web services. A DoS/DDoS attack completely blocks critical corporate IT services, which can be the Internet uplink, email server services, remote office connections or any other services such as online sales. Web-based attacks usually address data integrity and availability. Here, even inconspicuous web services can be abused for malware distribution or web form data theft through manipulated web links.
14. Targeted attacks (APTs)
The big difference between a “normal” hacking attack on an infrastructure and an Advanced Persistent Threat (APT) is that APT attacks are highly targeted and carried out with a high level of effort. To this end, the attackers sometimes spend weeks researching employee responsibilities and existing customer and supplier relationships before the attack is launched. Customized malware is also often developed for an APT attack, which is not detected by commercially available malware protection programs. APT attacks are often primarily designed for long-term spying on the victims (Link WIKI: Industrial espionage).
15. Attacks on SSL encryption
Attacks on SSL encryption are concerned on the one hand with the danger posed by self-signed certificates, which can be easily attacked via man-in-the-middle, and on the other hand with outdated, insecure cryptographic algorithms and key lengths that do not provide sufficient protection for transmission protocols. The use of OpenSSL in applications and web services in particular poses greater risks, since OpenSSL vulnerabilities (see Heartbleed, Poodle) are extensively documented and attackers immediately try to exploit them.
16. Attacking Web Applications (OWASP Top 10)
Do you develop web applications yourself? Then you should know the Open Web Application Security Project’s top 10 threats for this type of application: A1:2021 — Broken Access Control, A2:2021 — Cryptographic Failures, A3:2021 — Injection, A4:2021 — Insecure Design, A5:2021 — Security Misconfiguration, A6:2021 — Vulnerable and Outdated Components, A7:2021 — Identification and Authentication Failures, A8:2021 — Software and Data Integrity Failures, A9:2021 — Security Logging and Monitoring Failures, A10:2021 — Server-Side Request Forgery.
Unfortunately, new or existing web applications are not regularly scanned for these threats, making it far too easy for hackers to hijack web apps and harm the enterprise.
17. Zero-Day Attacks
In principle, a zero-day vulnerability is one of many vulnerabilities that are discovered, but the difference is that there is not yet a patch or hotfix for the vulnerability. In the early phase of a zero-day vulnerability, there is often no solid information about the extent and impact of the vulnerability. Companies are required to identify such zero-day vulnerabilities at an early stage. This requires a reliable zero-day information source and a quick assessment of whether affected services are used in the company.
Classification: TLP White
Creator: Andreas Schuster, SEC4YOU
Version: 1.0
Date: 8.7.2022